Security readiness cannot be fully measured through vulnerability scans or penetration testing alone. Organizations must also evaluate how well their teams detect, respond to, and manage real-world cyber incidents.
uMercs provides advanced security exercises designed to simulate realistic attack scenarios and test both technical defenses and organizational response capabilities.
Get a Free Dark Web Scan
Fill out the form below to get a dark web scan and find out if your data is on the dark web!
Purple Team Exercises
A Purple Team exercise brings together offensive security (red team) and defensive security teams (blue team) in a collaborative engagement designed to improve detection and response capabilities.
Rather than simply attempting to breach systems, purple team engagements focus on continuous collaboration between attackers and defenders. As offensive techniques are executed, defensive teams observe, analyze, and improve their monitoring, alerting, and response processes in real time.
Purple teaming helps organizations:
- Improve threat detection and alerting capabilities
- Validate security monitoring and SIEM effectiveness
- Strengthen incident response procedures
- Reduce time to detect and respond to attacks
- Improve collaboration between security and operations teams
These exercises provide valuable insights into how well existing security controls perform against real-world attacker behavior.
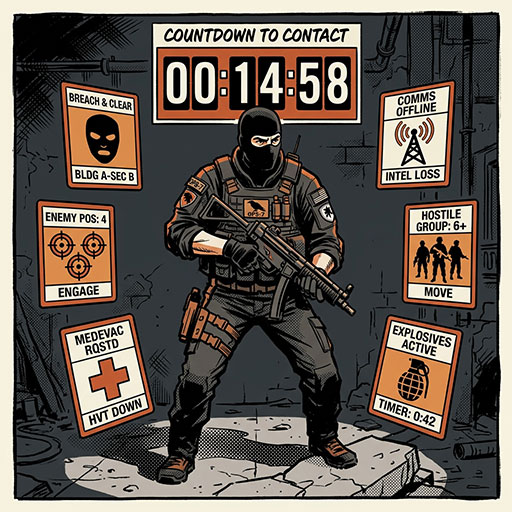
Tabletop Exercises (TTX)
Tabletop exercises (TTX) simulate real-world cyber incidents in a structured discussion format, allowing leadership and response teams to walk through how they would respond to a security crisis.
These exercises help organizations evaluate decision-making processes, communication strategies, and incident response procedures before a real attack occurs.
Tabletop exercises help organizations test:
- Incident response procedures
- Crisis communication plans
- Leadership decision-making during incidents
- Coordination between technical and executive teams
- Regulatory and breach notification requirements
By practicing these scenarios in advance, organizations can identify gaps in their response plans and improve preparedness for real cybersecurity incidents.

